1. Executive Summary
DarkMatter operates as an encrypted trading infrastructure hosted exclusively within the Tor hidden service network. Established to facilitate the exchange of digital goods and privacy-centric services, the platform has grown to become a prominent fixture in the decentralized web ecosystem.
From its inception, the architecture was designed around cryptographic resilience, demanding users employ advanced operations security (OpSec) protocols. Observers note that the platform heavily prioritizes anonymity over user experience, actively stripping away legacy web features in favor of lightweight, text-heavy cryptographic interactions.
2. Historical Timeline
Phase I: Foundation
The hidden service was initially detected by network analysts in late 2021. Early iterations featured a hybrid cryptocurrency model, supporting both Bitcoin and Monero, alongside basic two-factor authentication via PGP.
Phase II: Privacy Migration
Following the systemic tracing vulnerabilities associated with public ledgers, DarkMatter initiated a mandatory migration to a Monero-only (XMR) framework. This move entirely eliminated Bitcoin support, aligning the platform with strict anonymity standards.
Phase III: Advanced Infrastructure
Introduction of customized DDoS mitigation routing and robust multisignature (multisig) escrow nodes. DarkMatter implemented a decentralized mirror rotation system to preserve uptime during persistent network congestion attacks.
3. Technical Architecture
XMR Currency Protocol
Exclusive utilization of the Monero blockchain. The platform uses sub-addresses for deposit isolation, ensuring ring signatures and stealth addresses obfuscate the origin and destination of all financial routing.
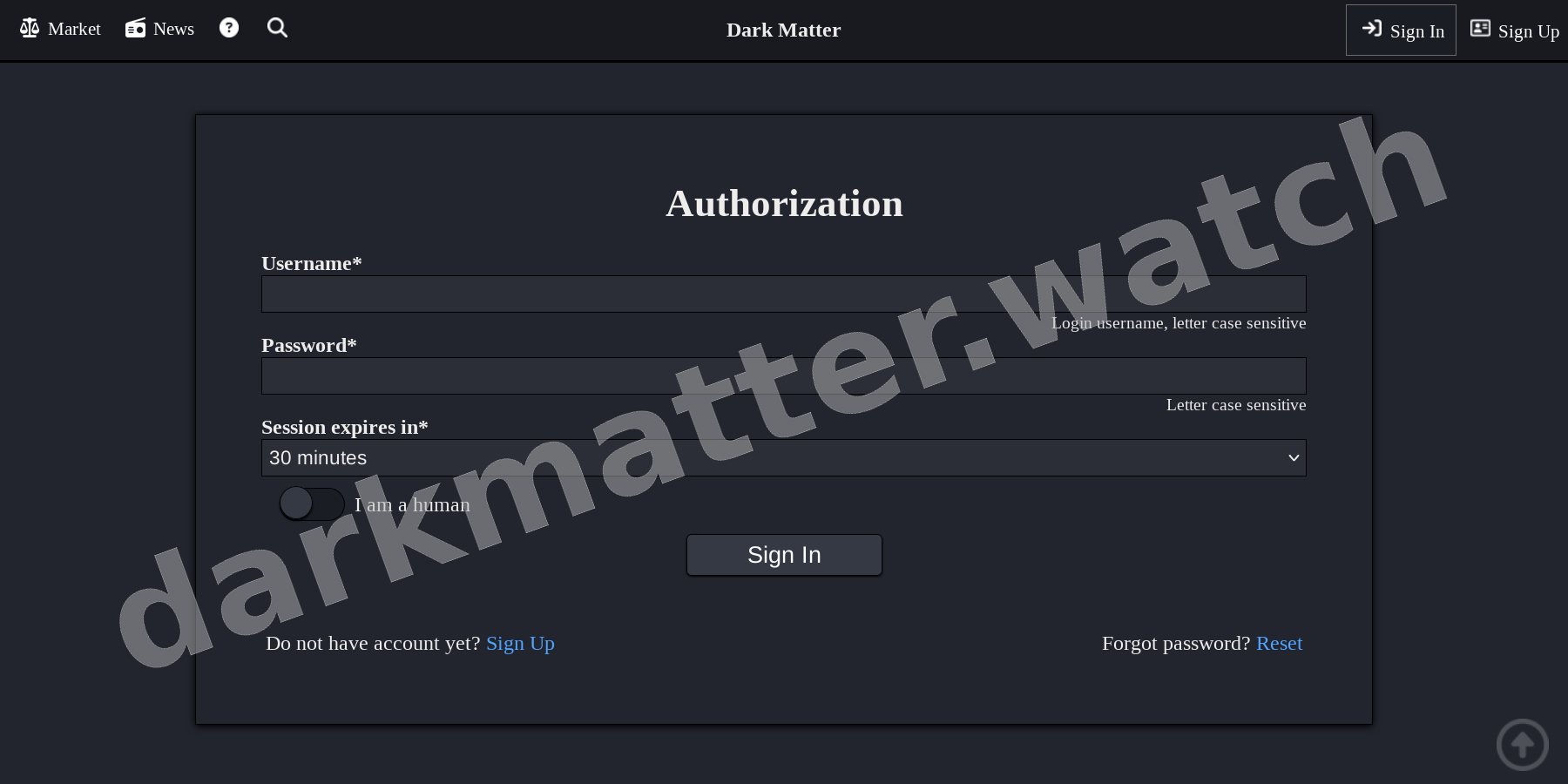
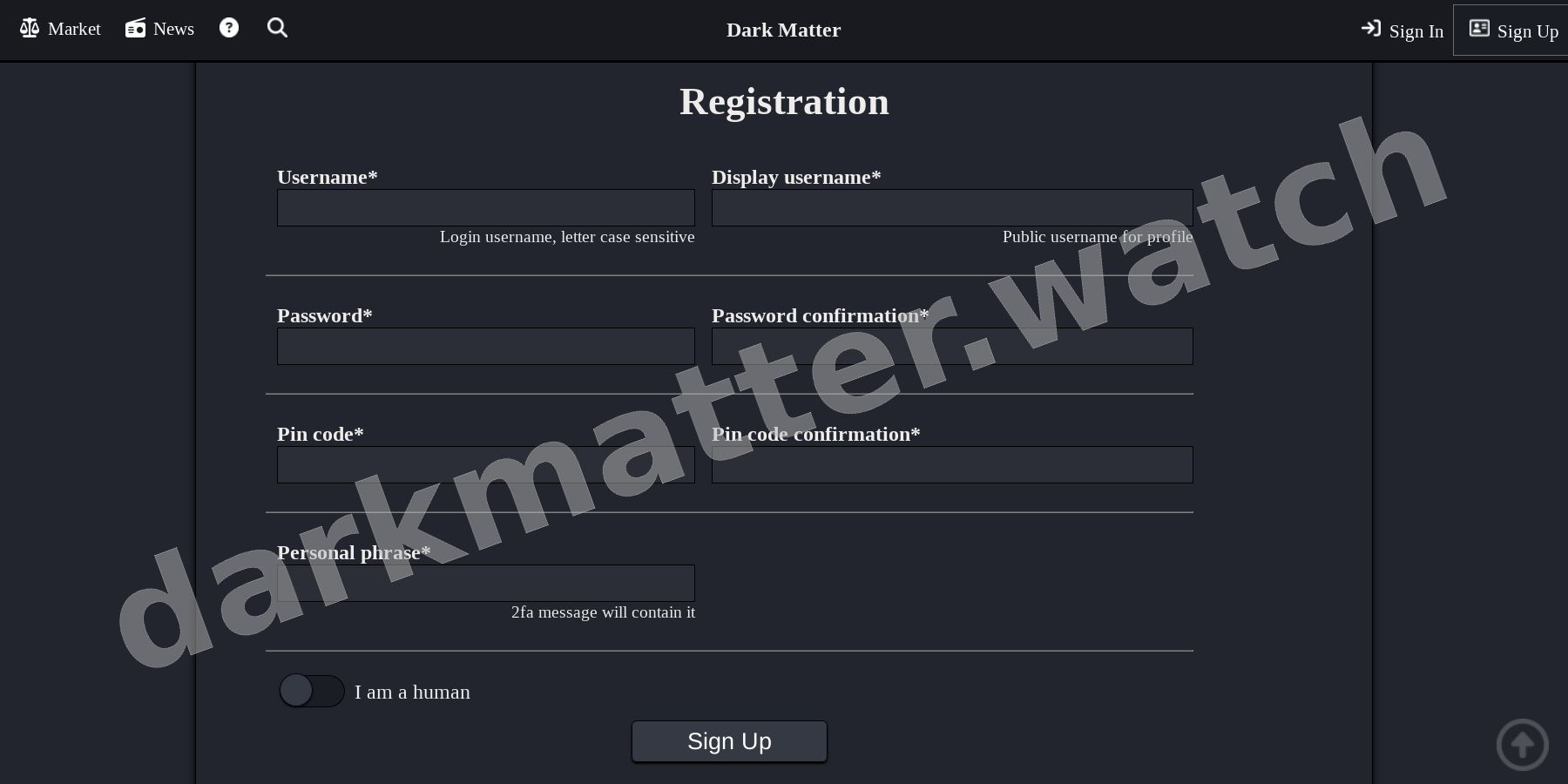
2FA Cryptographic Auth
Authentication is intrinsically tied to RSA-4096 PGP keys. Users must natively decrypt challenges to access accounts or authorize withdrawals, mitigating credential stuffing attacks entirely.
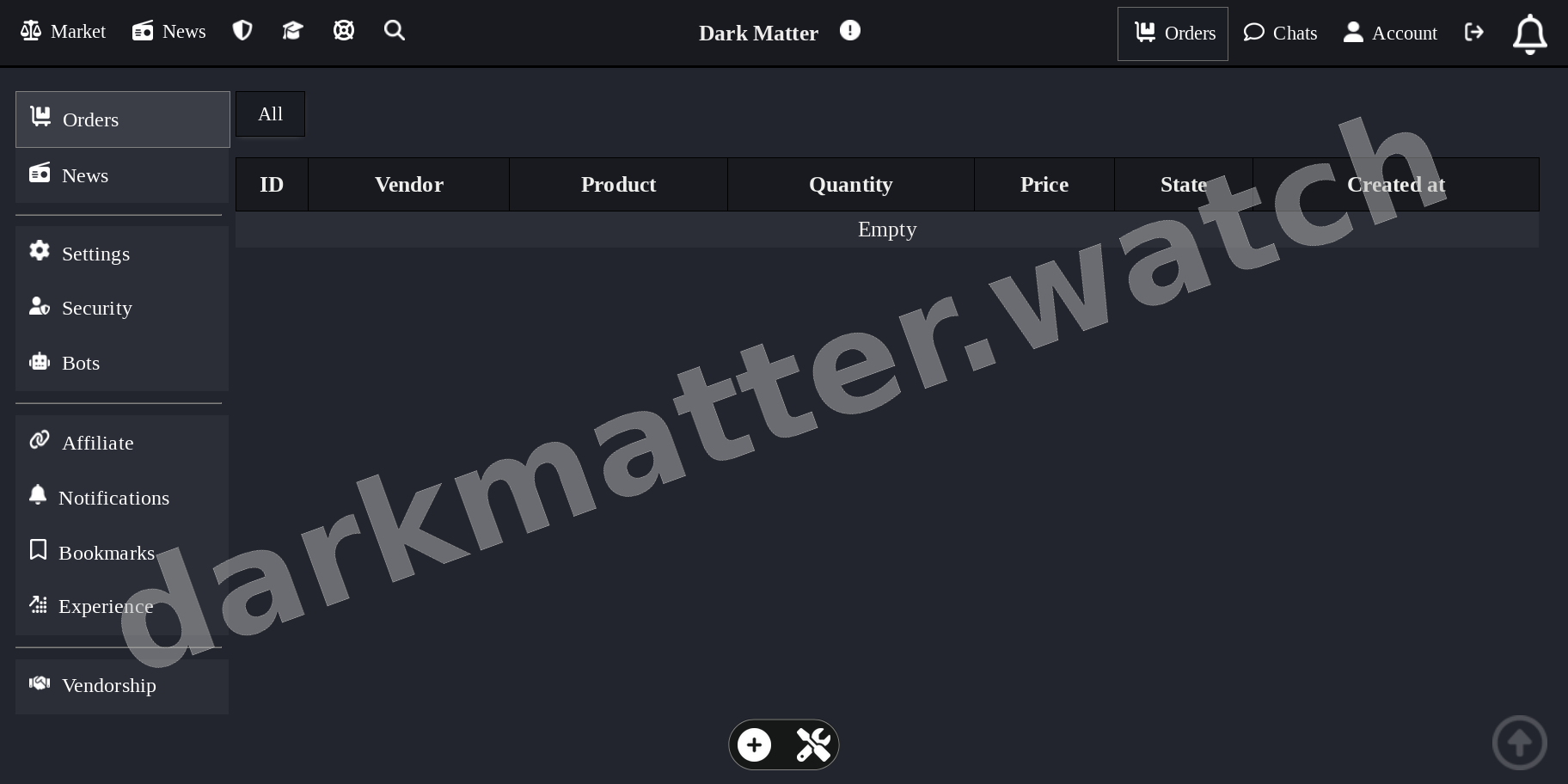
ESC Escrow & Multisig Routing
The escrow mechanics operate efficiently by holding funds in a centralized smart-contract-like state until final physical or digital delivery is attested. More advanced participants utilize 2-of-3 multisig setups, requiring cryptographic cooperation between the merchant, the purchaser, and a platform adjudicator, thereby enforcing a zero-trust financial environment.
Community & Statistics
- Estimated Active Nodes 450,000+
- Merchant Verification Strict Bond Requirement Suppliers must post significant collateral and prove cross-platform cryptographic identity to initiate operations.
-
Dispute Resolution Rate
94% Automated
- General Reputation Systemically Reliable
Research Directive
All data provided in this historical overview is sourced from public darknet intelligence streams, cross-referenced PGP signatures, and independent blockchain analysis nodes.
Researchers are reminded to maintain isolated operating systems (e.g., TailsOS or Whonix) when verifying the operational status of any cryptographic infrastructure discussed herein.
4. Platform Interface Preview